Unleashing the Power of Traceability in Cloud Security: A Comprehensive Guide
Welcome to the digital revolution, where cloud computing is the new normal, transforming businesses by offering computing resources at your fingertips. But as we embrace the cloud, we also encounter a new breed of security challenges. Among these, traceability stands out as a critical player in the arena of cloud security. This article will take you on a journey through the world of traceability, highlighting its importance, its role in combating security threats, and how to build an effective traceability framework.
Decoding Traceability in Cloud Security
Imagine having a superpower that allows you to monitor and track every activity and change within your cloud ecosystem. That’s what traceability in cloud security is all about. It’s like having a magnifying glass that scrutinizes log data and metrics, providing real-time insights into system events. From tracking user activity and system modifications to monitoring network traffic, traceability is your first line of defense, enabling rapid detection and neutralization of security threats.
Why Traceability is a Game-Changer in Cloud Security
Traceability wears two hats in the realm of cloud security. First, it’s your security detective, helping organizations spot and tackle security threats as they happen. While traditional on-site environments have clear-cut boundaries making it easier to detect security incidents, the cloud is a different beast altogether. Its ambiguous boundaries and diverse locations make timely detection and resolution a bit of a challenge, but traceability is up to the task.
Second, traceability is your compliance officer. With a myriad of regulations and standards requiring organizations to demonstrate compliance with security policies, traceability steps in to provide a detailed audit trail of all activities in the cloud ecosystem. This makes compliance audits a breeze and ensures accountability is never compromised.
Building a Traceability Framework: Your Step-by-Step Guide
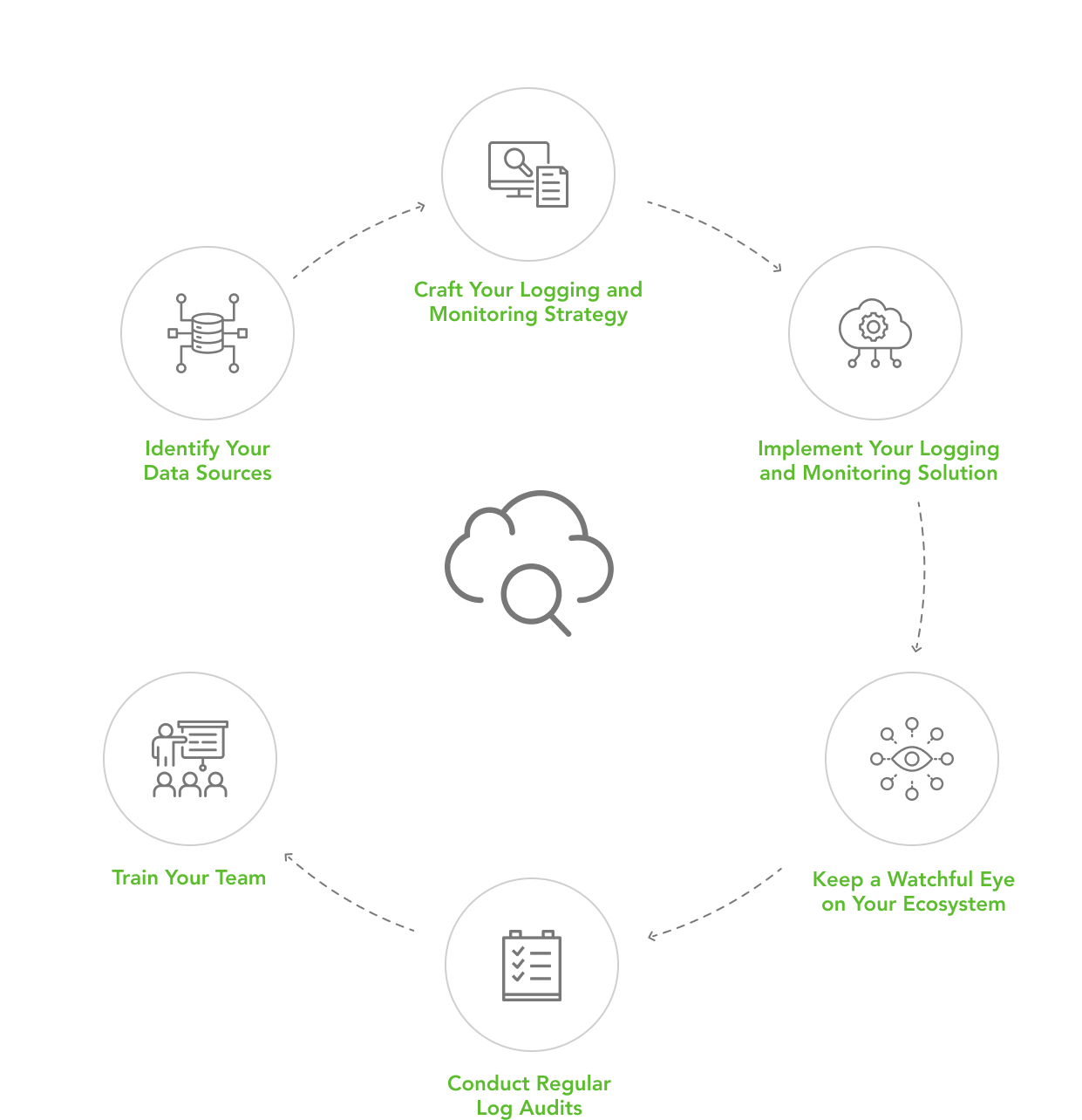
To harness the power of traceability, you need a well-thought-out logging and monitoring strategy. Here’s how to go about it:
Step 1: Identify Your Data Sources: Start by mapping out all data sources in your cloud ecosystem, including applications, databases, network devices, and cloud services. Understand the logs and metrics each source offers and devise a plan to collect them.
Step 2: Craft Your Logging and Monitoring Strategy: Decide what data to collect, how often, and where to store it. Also, establish an alert and notification strategy to swiftly tackle security incidents.
Step 3: Implement Your Logging and Monitoring Solution: Bring your strategy to life by integrating logging and monitoring tools with your cloud environment. Set up alert and notification systems to respond quickly to security threats.
Step 4: Keep a Watchful Eye on Your Ecosystem: Monitor your cloud environment round the clock. Analyze log and metric data to spot security incidents and take corrective action. Remember to keep your logging and monitoring strategy updated for continued effectiveness.
Step 5: Conduct Regular Log Audits: Regular log audits are essential to ensure your traceability measures are up to par. These audits can reveal gaps in your strategy and provide valuable insights for improvement.
Step 6: Train Your Team: A well-trained team that understands the importance of traceability and can effectively use the tools is a key asset. Keep them in the loop with regular training sessions on the latest logging and monitoring best practices.
In the ever-evolving landscape of cloud computing, traceability isn’t just a nice-to-have; it’s a must-have. A robust traceability framework allows organizations to identify and resolve security threats in real-time while meeting compliance requirements. It offers a clear view of the cloud environment, enabling organizations to respond effectively to security incidents. With the right tools, strategies, and a well-trained team, you can bolster your cloud security, ensuring accountability and transparency are at the heart of your operations.






